Software patches are essential safeguards that fix security holes, resolve bugs, improve compatibility across diverse environments, and help organizations maintain trusted, up-to-date software stacks. In a mature approach to IT operations, software patch management coordinates discovery, impact assessment, testing, approval, and deployment to reduce risk, demonstrate accountability, and maintain regulatory compliance. When managed well, these patches minimize exposure time, close backdoors, and guard critical assets without unnecessarily disrupting end users or business processes while maintaining a clear chain of custody. Patch deployment strategies should balance rapid remediation with thorough validation, ensuring changes are applied safely, auditable, and traceable. This ongoing discipline also reinforces governance, supports visibility for security teams, and helps the organization adapt to evolving threats over time, ensuring continuity of service, reducing audit overhead, and building trust with customers and partners in a changing threat landscape.
In other words, these updates represent small, carefully tested changes that close gaps and improve software health. Organizations manage the lifecycle of these fixes through governance, asset inventories, change control, and audit trails to minimize risk. Vendors and IT teams may refer to them as security fixes, hotfixes, remediation packages, or maintenance releases, depending on the platform and environment. A well-orchestrated rollout combines testing, phased deployment, and rollback planning to preserve uptime while addressing vulnerabilities. Ultimately, the goal is to sustain stability as new versions arrive and threats continue to evolve.
What Are Software Patches and How They Protect Your Systems
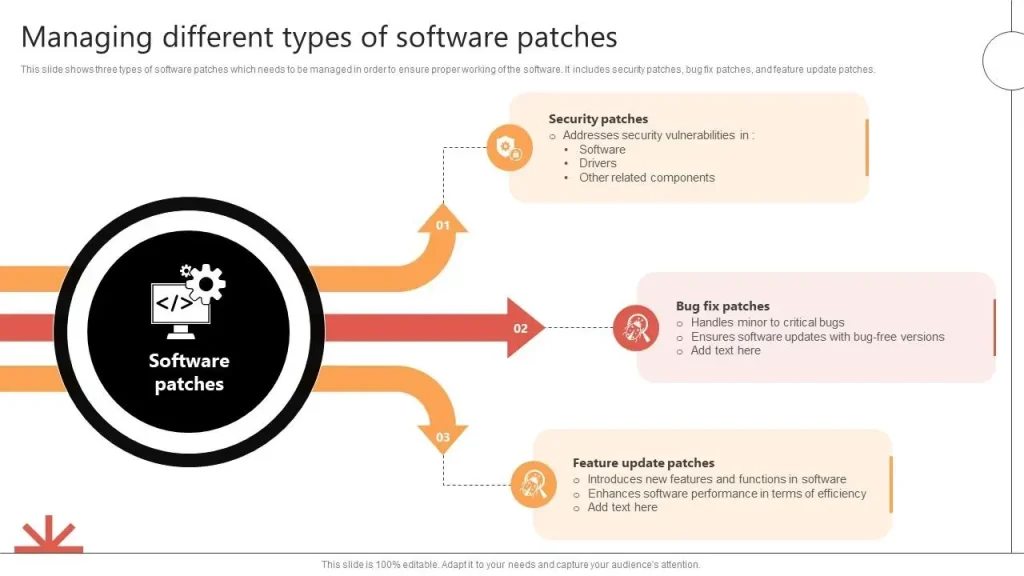
Software patches are targeted code changes that fix security holes, resolve bugs, and improve compatibility. They can be small hotfixes or larger rollups released by vendors to address issues discovered after a product’s release. Understanding Software patches helps organizations appreciate how a timely update reduces risk, strengthens defenses, and maintains reliable operations across diverse environments.
By applying patches, teams close entry points that attackers could exploit, prevent data loss from defects, and ensure software behaves as intended. Effective patch management translates these fixes into concrete security and reliability gains, supporting compliance with industry standards and reducing the likelihood of outages caused by unpatched vulnerabilities.
The Patch Lifecycle: Discovery to Deployment
A structured patch lifecycle begins with discovery and inventory, when teams identify what software is in use and which systems need patches. This step lays the groundwork for risk-based prioritization and ensures that vulnerable versions are detected across endpoints, servers, and cloud services.
From there, assessment, testing, deployment, and verification follow. Testing in a staging environment helps catch compatibility issues, while change control and rollback plans minimize disruption. Automated or semi-automated deployment supports scale, but ongoing verification confirms that patches are applied correctly and vulnerabilities are mitigated.
Security Patches vs. Vulnerability Patches: Prioritizing Risk
Security patches address exploitable vulnerabilities that could allow unauthorized access, data theft, or service disruption. When a patch fixes a vulnerability with a known exploit, prioritizing its deployment becomes critical to minimize exposure time and reduce the attack surface.
Vulnerability patches are the broader category of fixes that close flaws discovered through testing, monitoring, or threat intel. A mature patching program applies risk-based prioritization and business impact analysis to determine which vulnerabilities warrant immediate attention and which can follow standard patching cadences within patching best practices.
Patch Deployment Strategies: Safe and Efficient Rollouts
Patch deployment strategies guide how updates are rolled out to minimize downtime and prevent breakages. Techniques such as staged rollouts, canary releases, and scheduled maintenance windows help detect issues early and limit the blast radius of any problem.
Organizations should pair deployment strategy with monitoring, rollback plans, and vendor guidance. Clear communication with stakeholders and end users ensures expectations are managed while automation handles detection, download, and installation in a controlled, auditable manner.
Software Patch Management: Practices, Tools, and Governance
Software patch management is the structured process of acquiring, testing, deploying, and verifying patches across an organization. This practice aligns stakeholders, defines roles, and establishes governance to ensure patches are applied in a timely, controlled manner.
Effective patching relies on inventory accuracy, risk-based prioritization, tested change control, automated deployment with oversight, and robust verification. By implementing patching best practices and integrating with ITSM and security workflows, organizations can sustain consistent patch coverage and reduce residual risk.
Measuring Success: Patching Metrics, Compliance, and Continuous Improvement
To prove progress and maintain accountability, teams track metrics such as time-to-patch, patch coverage, failure rates, and audit readiness. These indicators support regulatory compliance and demonstrate how well the patch program reduces exposure and improves resilience.
Continuous improvement relies on governance, regular reviews, and updated tooling. Dashboards, reporting, and ongoing training ensure staff stay aligned with patching best practices, maintain a robust software patch management posture, and adapt to evolving threats and software ecosystems.
Frequently Asked Questions
What are Software patches and how does software patch management improve security and reliability?
Software patches are targeted code updates that fix security vulnerabilities, resolve bugs, and improve compatibility. Effective software patch management helps by maintaining an accurate inventory, testing patches in a staging environment, deploying them in a controlled rollout, and verifying that fixes are applied, which reduces risk and boosts system reliability.
Why are security patches critical and what is the recommended response time for applying them?
Security patches address known vulnerabilities that attackers could exploit. They should be prioritized based on risk and urgency, and organizations should apply them promptly using established patching best practices to minimize exposure time.
What are effective patch deployment strategies to minimize downtime and disruption?
Patch deployment strategies such as staged rollouts, canary updates, scheduled maintenance windows, and rollback plans help limit disruption and catch issues early. These approaches support timely remediation while preserving business operations.
What are patching best practices for enterprise software patch management?
Patching best practices include keeping a current software inventory, prioritizing patches by risk, testing patches in a sandbox, automating deployment with governance, and validating success after deployment. Documentation and monitoring ensure compliance and ongoing improvement.
How do vulnerability patches differ from feature patches within Software patches?
Vulnerability patches fix security holes and should be prioritized to reduce exposure, while feature patches implement enhancements or fixes and may follow a slower cadence. A mature patching program treats both with appropriate governance and testing.
How can organizations measure the success of software patch management?
To measure success, track metrics such as time-to-patch, patch coverage, reduction in exposure, and post-deployment verification results. Regular dashboards, audits, and incident reductions demonstrate improved security, reliability, and compliance.
| Topic | Key Points |
|---|---|
| What are Software patches? | Small code changes released by vendors to fix security holes, resolve bugs, and improve compatibility. They aim to mitigate risk, restore expected behavior, and maintain compatibility. |
| Patch Types | Patches come in two broad categories: security patches (urgent to fix vulnerabilities) and feature/bug-fix patches (improvements or fixes requested by users). Priority is usually higher for security patches. |
| Patch Lifecycle Phases | Discovery → Inventory; Assessment → Prioritization; Testing → Change control; Deployment → Rollout; Verification → Validation; Documentation → Auditing. |
| Patch Management | An ongoing discipline: maintain inventory, prioritize by risk, test changes, deploy with oversight, and verify outcomes to ensure governance and compliance. |
| Why They Matter | Security risk reduction, regulatory compliance, improved stability and reliability, potential performance gains, and better ecosystem compatibility. |
| Deployment Strategies | Staged/ phased rollouts, canary releases, scheduled maintenance windows, rollback plans, and clear vendor/user communications to minimize disruption. |
| Best Practices | Policy and roles, current asset inventory, risk-based prioritization, testing in staging, automated deployment with oversight, post-deployment verification, rollback planning, and staff training. |
| Common Pitfalls | Incomplete inventories, rushing patches without testing, patching legacy systems, over-reliance on manual processes, weak change management, and poor stakeholder communication. |
| Tools & Real-World Use | Tools should provide coverage for OS/app/cloud environments, automation, testing/rollback features, reporting, and integration with IT workflows; real-world practice involves staged deployments and documentation. |
Summary
Conclusion: Software patches are a foundational element of modern IT. Understanding what patches do, why they matter, and how to implement them effectively through software patch management and thoughtful patch deployment strategies is crucial for protecting data, systems, and operations. With a proper patching framework in place, teams can navigate the patching lifecycle with confidence, minimize disruption, and reap the benefits of more secure, stable, and efficient software ecosystems.