Software patches are essential updates that fix vulnerabilities and bugs, helping protect computers and networks from evolving threats. Effective patch management means more than applying fixes; it is a disciplined process that aligns with risk, operations, and compliance. Security patches address exploitable weaknesses, reducing the window attackers have to compromise systems. Automatic updates can accelerate patch delivery while maintaining control, provided testing and change management stay in place. By understanding how software patches protect systems, organizations boost resilience and earn greater trust from users.
In other words, keeping software current means applying patches, fixes, and updates across devices. This practice connects to vulnerability management, risk reduction, and controlled change processes that defend endpoints. Mapping these ideas to actions such as inventorying assets, assessing exposures, testing changes, and validating deployments helps build a robust patch program.
Software Patches: What They Are and Why They Matter
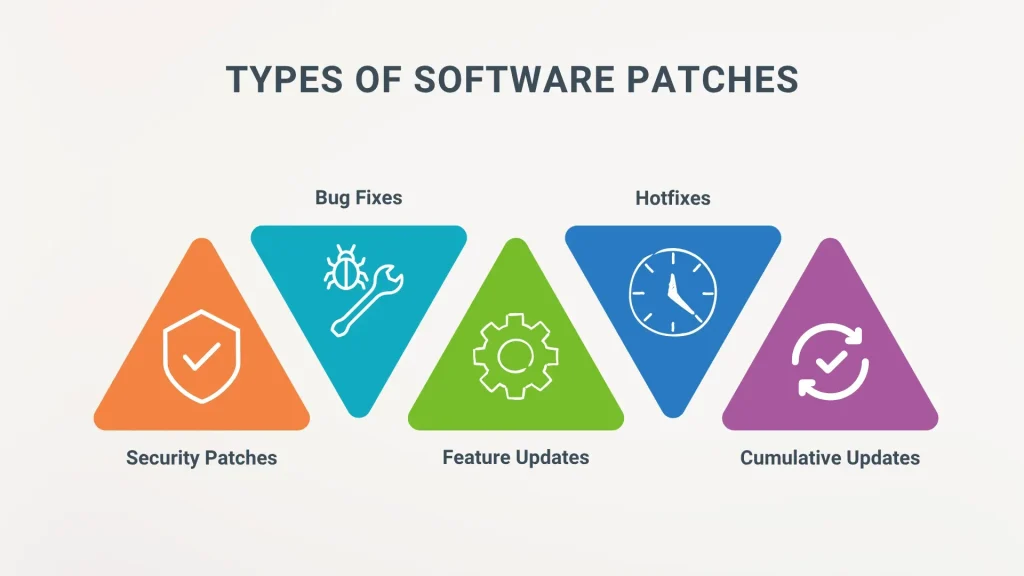
Software patches are small, targeted code updates released by vendors to fix vulnerabilities and bugs across operating systems, applications, and firmware. They represent the primary mechanism for keeping software environments secure and reliable, and they form a core part of every effective patch management strategy.
By applying patches promptly, organizations close security gaps, improve stability, and ensure compatibility with newer features. Understanding the role of software patches helps teams prioritize updates and align patching activities with business goals and risk tolerance.
Patch Management Best Practices for Modern IT Environments
Effective patch management involves discovering every asset, assessing risk, testing updates in a controlled staging environment, and coordinating deployment with minimal user disruption. A structured lifecycle ensures patches are not skipped or delayed due to busy schedules.
A mature program aligns patch activity with business risk, scales to organizational size, and incorporates verification, audit reporting, and continuous improvement. Clear ownership and measurable goals help sustain momentum across diverse systems.
Security Patches and Vulnerability Management: A Critical Priority
Security patches are a key subset of patches that target exploitable flaws and are central to a robust vulnerability management program. Prioritizing these updates reduces the window of opportunity for attackers and strengthens overall risk posture.
Coupling proactive vulnerability scanning with timely patch deployment minimizes exposure, supports compliance requirements, and helps security teams demonstrate concrete remediation progress across the environment.
Automatic Updates: Balancing Speed and Control
Automatic updates simplify maintenance by delivering patches directly to devices, which speeds up remediation and ensures consistency across endpoints. This approach is especially valuable for widely deployed software and systems with frequent vulnerability disclosures.
However, automation can reduce control and visibility if left unchecked. A balanced strategy typically prioritizes automated patching for less critical systems while enforcing testing, scheduled windows, and change reviews for mission-critical infrastructure.
Why Software Updates Are Essential for Compliance and Risk Reduction
The importance of software updates extends beyond immediate risk reduction; timely updates support compliance programs, industry standards, and data protection requirements. Regular patching demonstrates due diligence and helps avoid regulatory penalties.
By reducing the likelihood of breaches and service disruptions, software updates contribute to stronger governance and more predictable operation. Organizations can track metrics such as time-to-patch to quantify improvements in resilience.
Practical Steps to Build an Effective Patch Policy
Practical steps to build an effective patch policy include defining clear roles and responsibilities, establishing a predictable patch schedule, and maintaining an accurate asset inventory with versions and patch levels. These foundations enable targeted decision-making and faster response when new vulnerabilities emerge.
The policy should include testing standards and a staging environment, rollback options, and integration with change management and incident response. Ongoing monitoring and reporting show how software patches protect systems and contribute to long-term IT resilience.
Frequently Asked Questions
What are software patches and how does patch management help keep systems secure?
Software patches are small code updates released by vendors to fix security flaws and bugs. Patch management is the process of discovering, testing, deploying, and verifying patches across an environment to reduce risk and maintain system reliability. Regular patching of software patches is a core defense against exploits and outages.
What are security patches and why is the importance of software updates emphasized in patch management?
Security patches fix known vulnerabilities that attackers could exploit. They are a subset of software patches, and their timely deployment is essential. Effective patch management prioritizes security patches, tests compatibility, and deploys them to reduce risk and meet compliance.
How do automatic updates fit into patch management, and what are the trade-offs for enterprise systems?
Automatic updates deliver patches directly to devices, speeding protection and reducing manual effort. For enterprises, this can mean less control and potential downtime, so a balanced approach combines automatic deployment for low-risk patches with tested, scheduled updates for critical systems through patch management.
How do software patches protect systems from threats?
Software patches close security holes and fix bugs, reducing the risk of data loss, malware infection, and outages. A mature patch management process ensures patches are discovered, validated, and deployed promptly, maintaining security controls and system stability.
What is the patch management lifecycle and how does it support compliance and risk reduction?
The patch management lifecycle includes discovering assets, assessing risk, testing, planning deployment, verifying, and reporting. This process aligns with business risk and security standards, helping organizations demonstrate due diligence and reduce exposure through software patches.
What are common myths about patches and how should organizations approach patching effectively?
Common myths include patching always causes downtime or slows systems. In reality, patches can be tested and staged to minimize impact, and ignoring patches increases risk. An effective approach uses patch management automation, automatic updates where appropriate, risk-based prioritization, testing, rollback options, and clear change control.
| Section | Key Points | Notes |
|---|---|---|
| What are software patches? |
|
Intro |
| Patch types and release cycles |
|
Overview |
| Why regular updates matter |
|
Security importance, compliance, and ongoing risk management |
| Patch management explained |
|
Process overview and alignment with risk |
| The patch management lifecycle |
|
Six-step lifecycle |
| Best practices for effective patch management |
|
Risk-based and process-focused tips |
| Automatic updates and their role |
|
Automation benefits and caveats |
| The broader context: security patches and vulnerability management |
|
Security context and resilience |
| Common myths and myths busted |
|
Myth vs. reality |
| Practical steps to establish a patch policy |
|
Policy steps |
| Why patches contribute to a safer system |
|
Safety and resilience rationale |
| Real world examples of patching in action |
|
Practical outcomes |
Summary
Software patches are essential for keeping systems secure and up to date across devices and environments. An effective patch management program prioritizes critical vulnerabilities, tests for compatibility, and ensures software patches are deployed across the IT landscape. These practices reduce risk, support regulatory compliance, and strengthen resilience by preventing data loss, downtime, and breaches. By treating patching as a core IT discipline rather than a reactive task, organizations improve security posture and maintain trust with customers through timely, well-managed software patches.