Software patches are the small updates that software vendors release to fix security holes, resolve bugs, and improve performance, and they form a cornerstone of ongoing software hygiene for modern organizations. For many organizations, keeping systems up to date with patches is essential for reducing risk, yet patching can feel complex, time-consuming, and resource-intensive, especially in environments with diverse platforms and critical uptime requirements. This guide helps demystify patching, explains why patches matter, and outlines practical steps for managing patches across an organization, from discovery to verification and reporting. By adopting a structured approach such as patch management and patch deployment strategies, teams can minimize disruption while closing security gaps and maintaining governance, audit trails, and compliance with internal and external standards. From identifying vulnerable software to validating updates and monitoring outcomes, a disciplined patching program supports ongoing risk reduction and reliable operations to minimize operational risk and align with broader cybersecurity goals.
In other terms, these updates are part of an ongoing software maintenance cycle designed to close identified weaknesses and keep systems functioning smoothly. Rather than just fixes, organizations view these releases as a controlled process that reduces risk, ensures compatibility, and supports compliance. A modern approach to update governance emphasizes discovery, testing, staged rollout, and verification—echoing the core ideas of patch management without relying on the exact label. By thinking in terms of vulnerability mitigation, maintenance releases, and update orchestration across cloud, on-premises, and hybrid environments, teams can communicate clearly with stakeholders and build resilient defenses.
Understanding the Purpose of Software Patches in Modern IT
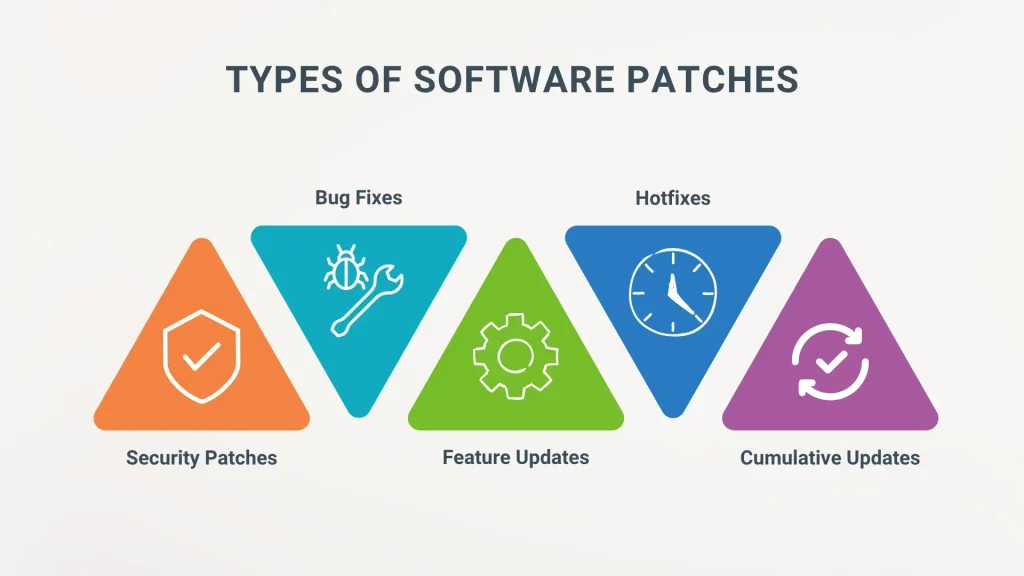
Software patches are small updates released by vendors to fix security holes, address bugs, and improve performance. This is the core reason organizations pursue a robust patch management program, and it highlights the importance of the software patching process in reducing risk across the environment. By regularly applying these patches, teams can close gaps that attackers might exploit and maintain healthier, more secure systems.
Beyond security, patches also improve stability and compatibility with other software, helping to prevent operational disruptions. Emphasizing the role of security patches in the broader security posture, organizations can align patching activities with vulnerability remediation goals, ensuring that critical flaws are prioritized and resolved before they can be exploited.
The Patch Management Lifecycle: From Discovery to Verification
A formal patch management lifecycle guides how patches are identified, assessed, tested, deployed, and finally verified. This lifecycle relies on precise asset inventories, patch metadata, and governance to ensure nothing is missed and every update is tracked alongside its potential impact. The process integrates SBOMs and vulnerability feeds to create a clear map of exposure across the organization.
Each stage supports risk-based decision-making and traceability. Testing and change control establish a controlled path for deployment, helping prevent regressions and enabling rollback if needed. This disciplined approach reinforces the overall patch deployment strategies and ensures that remediation efforts are both effective and auditable.
Security Patches and Vulnerability Remediation: Priorities and Practices
Security patches are typically the highest priority within the patch management ecosystem, designed to close known vulnerabilities before they can be exploited. Focusing on vulnerability remediation requires rapid assessment of exploit prevalence, affected assets, and the potential impact on sensitive data or critical services.
Effective remediation balances speed with safety through risk-informed prioritization and testing. Aligning patching activities with regulatory requirements and vendor advisories helps ensure compliance while maintaining system availability. Regularly updating stakeholders about risk posture and patch status reinforces governance and accountability.
Patch Deployment Strategies: From Canary to Automated Rollouts
Patch deployment strategies span from small, phased canary deployments to broad, automated rollouts. A phased approach minimizes risk by limiting exposure during initial deployment and provides early visibility into potential issues in complex, interconnected environments.
Automation, when paired with governance, can dramatically accelerate remediation across large fleets. A blended model—manual review for high-risk systems plus automated patching for standard workloads—often delivers the right balance between speed and control, while staged rollouts help ensure business continuity.
Cross-Environment Patch Management: On-Premises, Cloud, and Hybrid
Different environments present distinct patching challenges, from agent-based on-premises deployments to API-driven cloud patching. A unified patching strategy must accommodate these variations, ensuring policy enforcement and consistent risk mitigation across all platforms.
Effective patch management in diverse environments relies on centralized dashboards, standardized change controls, and integrated tooling. By harmonizing processes across on-premises, cloud, and hybrid setups, organizations can maintain a coherent security posture and simplify ongoing vulnerability remediation.
Measuring Success: Metrics, Reporting, and Continuous Improvement
Measuring patch management effectiveness involves key metrics such as time-to-patch, patch deployment success rate, mean time to patch, and compliance levels. Tracking these indicators provides visibility into remediation velocity and helps identify bottlenecks that slow vulnerability remediation.
Ongoing reporting supports governance and continuous improvement. Regular reviews of metrics, combined with automation and feedback from security and operations teams, enable refinements to patch management programs, enhancing resilience against threats and reducing the likelihood of disruption from future patches.
Frequently Asked Questions
What is patch management and how does it support the software patching process?
Patch management is the formal lifecycle of discovering, prioritizing, deploying, and verifying patches across an organization. It supports the software patching process by ensuring patches are applied promptly in a controlled way, reducing security risk and downtime.
In the software patching process, how should organizations handle discovery and inventory to prioritize security patches?
Begin with a complete discovery and inventory of hardware, software, and versions. This visibility enables prioritizing security patches based on risk, asset criticality, and exploit exposure.
What are best practices for deploying security patches without disrupting operations, and how do patch deployment strategies help?
Use patch deployment strategies that feature phased rollouts, maintenance windows, and automated validation. Combine testing, rollback plans, and monitoring to minimize user impact while maintaining security.
How can organizations align vulnerability remediation with patch deployment strategies to close exposure quickly?
Prioritize patches for high-risk systems and active vulnerabilities as part of vulnerability remediation, then validate in controlled environments before broad rollout. Automate where safe, enforce change control, and monitor results to reinforce security posture.
What considerations differentiate patch deployment strategies for on-premises vs cloud and hybrid environments?
Patch deployment strategies must account for environment differences, such as agents, patching APIs, and centralized dashboards. A unified policy with environment-aware controls ensures consistent patching and governance across all infrastructures.
What metrics should be monitored to measure the effectiveness of patch management and vulnerability remediation?
Track time-to-patch (TTP), mean time to patch (MTTP), deployment success rate, and overall compliance. Regularly reviewing these metrics helps assess progress and drive improvements in vulnerability remediation.
| Topic | Key Points |
|---|---|
| What software patches do? |
|
| Why patches matter |
|
| The patch management lifecycle |
|
| Discovery and inventory |
|
| Assessment and prioritization |
|
| Testing and change control |
|
| Deployment and rollout |
|
| Verification and reporting |
|
| Patch management strategies |
|
| Security patches and vulnerability remediation |
|
| Tools, best practices, and metrics |
|
| Real-world considerations and pitfalls |
|
| A practical case study (illustrative) |
|
Summary
Software patches are essential for security; software patches help reduce risk by fixing vulnerabilities, addressing bugs, and improving performance. This descriptive overview summarizes what patches do, why they matter, and how to manage them effectively across an organization. By following a structured patch management lifecycle—discovery, assessment, testing, deployment, and verification—and applying appropriate deployment strategies and automation where suitable, organizations can minimize downtime, stay compliant, and strengthen their security posture. With clear governance, ongoing measurement, and a culture that prioritizes timely remediation, patching becomes a strategic capability rather than a perpetual headache. In short, software patches are a critical, ongoing investment in resilience and trust.